In computer networking, switches are devices that forward data packets between network segments. They operate at the data link layer (layer 2) and network layer (layer 3) of the OSI model.
Layer 2 switches, also known as data link layer switches, work at the data link layer of the OSI model. They use MAC (Media Access Control) addresses to forward packets within a single broadcast domain. Layer 2 switches do not make any decisions based on the IP addresses of the packets, which means they do not have the ability to route packets between different subnets.
Layer 3 switches, also known as network layer switches, work at the network layer of the OSI model. They use IP addresses to forward packets between different subnets. This means that layer 3 switches have routing capabilities and can make decisions about where to forward a packet based on its destination IP address.
One key difference between layer 2 and layer 3 switches is that layer 3 switches can route traffic between different VLANs (Virtual LANs) on the same device, while layer 2 switches can only switch traffic within the same VLAN. This means that layer 3 switches can provide inter-VLAN routing, while layer 2 switches cannot.
Another key difference is that layer 3 switches typically have more advanced features such as Quality of Service (QoS), Access Control Lists (ACLs), and Multicast support. They are also more expensive than layer 2 switches.
In summary, layer 2 switches work at the data link layer of the OSI model and use MAC addresses to forward packets within a single broadcast domain. Layer 3 switches work at the network layer of the OSI model and use IP addresses to forward packets between different subnets, they have routing capabilities and can make decisions about where to forward a packet based on its destination IP address.
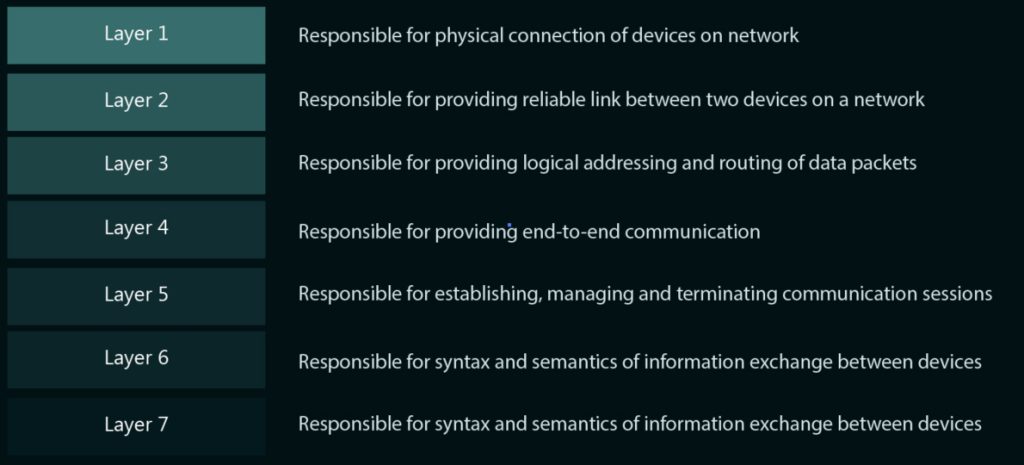
Now that we have established about the minor differences between layer 2 and layer 3 switches, lets take a look at what these layers are. How they develop sense in a layman’s view about the understanding of how layer 2 and layer 3 switches work. They work primarily on the OSI model which is the Open Systems Interconnection models divided into 7 layers.
Before we dive deeper, as a quick overview, please see the below matrix explaining in short what the different OSI-model layers are all about.
What are OSI Layers responsible for?
1. Physical Layer (Layer 1)
The physical layer of the OSI (Open Systems Interconnection) model is the first layer and is responsible for the physical connection of devices on a network. It defines the electrical, mechanical, and functional characteristics of the interface between a device and the transmission medium. This includes things such as voltage levels, signaling method, and connector types.
The physical layer is responsible for transmitting raw bits over the network media such as copper cables, optical fibers, or wireless transmissions. It converts the digital signals from the data link layer into analog signals for transmission and vice versa for reception. It also handles the synchronization of the signals, encoding, and modulation of the data for transmission.
Examples of devices that work at the physical layer include hubs, repeaters, and transceivers. Physical layer protocols include Ethernet, Token Ring, and FDDI. In short, the physical layer of the OSI model deals with the physical and electrical details of the network connection and is responsible for transmitting and receiving raw bits over the network media.
What are the services provided by the physical layer?
The physical layer of the OSI model provides several services that enable the successful transmission of data over a network. These services include:
- Data Transmission: The physical layer is responsible for converting digital signals from the data link layer into analog signals for transmission over the network media. It also handles the modulation of the data for transmission, allowing it to travel over the physical medium.
- Data Reception: The physical layer is responsible for receiving analog signals from the network media and converting them back into digital signals for the data link layer to process.
- Medium Access Control: The physical layer manages access to the shared network media. It coordinates the use of the medium by different devices to ensure that only one device can transmit at a time, avoiding collisions.
- Signal Encoding: The physical layer is responsible for encoding the data into a format that can be transmitted over the network media. This includes things such as voltage levels and signaling method.
- Signal Synchronization: The physical layer is responsible for synchronizing the transmission and reception of data between devices. This ensures that the data is transmitted and received at the correct rate, allowing the devices to communicate effectively.
- Media Connectivity: The physical layer is responsible for providing the physical connection between devices on a network. This includes things such as connector types and cable specifications.
- Error Detection and Correction: The physical layer is responsible for detecting and correcting errors that may occur during transmission over the network media. This ensures that the data is transmitted accurately and reliably.
In summary, the physical layer provides services that enable the successful transmission of data over a network. These services include data transmission and reception, medium access control, signal encoding, signal synchronization, media connectivity and error detection and correction.
Which protocols use physical layer?
The physical layer of the OSI model is responsible for the physical connection of devices on a network and the transmission of raw bits over the network media. Several protocols are used at the physical layer to control these functions and enable successful communication between devices. Some examples of these protocols include:
- Ethernet: This is one of the most widely used physical layer protocols. It defines the characteristics of the wired LAN (Local Area Network) connections, including the frame format, maximum cable length, and connector types. Ethernet uses the CSMA/CD (Carrier Sense Multiple Access with Collision Detection) mechanism to control access to the medium.
- Wi-Fi: Wi-Fi is a physical layer protocol that enables wireless communication between devices. It defines the characteristics of the wireless LAN connections, including the frequency bands, modulation techniques, and security mechanisms. Wi-Fi uses the CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance) mechanism to control access to the medium.
- Token Ring: This is another physical layer protocol that was used primarily in LANs. It uses a token-passing mechanism to control access to the medium, which ensures that only one device can transmit at a time.
- FDDI: Fiber Distributed Data Interface (FDDI) is a physical layer protocol that uses optical fibers as the transmission medium. It is capable of providing high-speed data transfer and is mainly used in backbone networks.
- RS-232: This is a physical layer protocol that defines the electrical and mechanical characteristics of the serial communication link. RS-232 is commonly used in applications such as point-of-sale terminals, and industrial control systems.
- USB: Universal Serial Bus (USB) is a physical layer protocol that defines the electrical and mechanical characteristics of the connection between computers and peripheral devices. USB is widely used to connect devices such as keyboards, mice, printers, and cameras.
Briefly, many protocols use the physical layer of the OSI model, some examples are Ethernet, Wi-Fi, Token Ring, FDDI, RS-232, and USB. Each protocol defines the characteristics of the physical connection and the method of controlling access to the medium.
2. Data Link Layer (Layer 2)
The data link layer of the OSI (Open Systems Interconnection) model is the second layer and is responsible for providing reliable link between two devices on a network. It provides the means for error-free transfer of data across the physical link established by the physical layer.
The data link layer takes the raw bits received from the physical layer and encapsulates them into frames. Each frame includes a header and a trailer that contains control information such as source and destination MAC addresses and error-checking codes. It also provides flow control and error-checking mechanisms to ensure that data is transmitted correctly and without errors.
The data link layer is divided into two sub-layers: the Media Access Control (MAC) layer and the Logical Link Control (LLC) layer. The MAC layer is responsible for managing access to the shared network medium, ensuring that only one device can transmit at a time and avoiding collisions. The LLC layer is responsible for providing a consistent interface to the network layer, regardless of the underlying MAC technology.
Examples of devices that work at the data link layer include switches and bridges. Data link layer protocols include Ethernet, Token Ring, and FDDI. The CISCO Catalyst 2960 and Catalyst 3750 Series are among the well known options of Layer 2 Switches.
In short, the data link layer of the OSI model provides a reliable link between two devices on a network by providing flow control and error-checking mechanisms, encapsulating the raw bits into frames, and managing access to the shared network medium through Media Access Control (MAC) and Logical Link Control (LLC) layers.
What are the services provided by Data Link Layer?
The data link layer of the OSI model provides several services that enable the successful transmission of data between two devices on a network. These services include:
- Framing: The data link layer is responsible for dividing the data received from the network layer into smaller units called frames. Each frame includes a header and a trailer that contains control information, such as source and destination MAC addresses and error-checking codes.
- Media Access Control: The data link layer manages access to the shared network medium. It ensures that only one device can transmit at a time and avoids collisions. This is achieved through different techniques such as CSMA/CD (Carrier Sense Multiple Access with Collision Detection) or Token Passing.
- Error Detection and Correction: The data link layer is responsible for detecting and correcting errors that may occur during transmission over the network media. It uses error-checking codes, such as cyclic redundancy check (CRC), to detect errors and retransmit frames if necessary.
- Flow Control: The data link layer is responsible for controlling the flow of data between devices. It ensures that the receiving device is able to handle the incoming data, and regulates the flow of data to prevent overloading the receiver.
- Link Management: The data link layer is responsible for managing the link between two devices. It establishes and terminates connections, monitors the link status, and performs other link-related functions.
- Addressing: The data link layer provides logical addressing, mainly through MAC addresses, which are unique and assigned to each device on a network. This allows for identification and communication between devices.
- Logical Link Control: The Logical Link Control (LLC) sublayer of the data link layer provides a consistent interface to the network layer, regardless of the underlying MAC technology. It also handles the flow and error control mechanisms, and some other types of management between different layers.
In summary, the data link layer provides services that enable the successful transmission of data between two devices on a network. These services include Framing, Media Access Control, Error Detection and Correction, Flow Control, Link Management, Addressing and Logical Link Control. These services are essential for the proper communication and coordination of devices on a network.
Which protocols use data link layer?
The data link layer of the OSI model is responsible for providing a reliable link between two devices on a network by managing the flow of data, providing error-checking mechanisms, and managing access to the shared network medium. Several protocols are used at the data link layer to control these functions and enable successful communication between devices. Some examples of these protocols include:
- Ethernet: This is one of the most widely used data link layer protocols. It defines the characteristics of the wired LAN (Local Area Network) connections, including the frame format, maximum cable length, and connector types. Ethernet uses the CSMA/CD (Carrier Sense Multiple Access with Collision Detection) mechanism to control access to the medium.
- Wi-Fi: Wi-Fi is a data link layer protocol that enables wireless communication between devices. It defines the characteristics of the wireless LAN connections, including the frequency bands, modulation techniques, and security mechanisms. Wi-Fi uses the CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance) mechanism to control access to the medium.
- Token Ring: This is another data link layer protocol that was used primarily in LANs. It uses a token-passing mechanism to control access to the medium, which ensures that only one device can transmit at a time.
- FDDI: Fiber Distributed Data Interface (FDDI) is a data link layer protocol that uses optical fibers as the transmission medium. It is capable of providing high-speed data transfer and is mainly used in backbone networks.
- PPP: Point-to-Point Protocol (PPP) is a data link layer protocol used to establish a link between two nodes over a serial cable, such as a telephone line or a cellular network.
- ATM: Asynchronous Transfer Mode (ATM) is a data link layer protocol used in high-speed networks. It uses fixed-length cells to transfer data and provides Quality of Service (QoS) guarantees.
In summary, many protocols use the data link layer of the OSI model, some examples are Ethernet, Wi-Fi, Token Ring, FDDI, PPP, and ATM. Each protocol defines the characteristics of the logical link between devices and the method of controlling access to the medium, and providing error detection and correction mechanisms.
3. Network Layer (Layer 3)
The network layer of the OSI (Open Systems Interconnection) model is the third layer and is responsible for providing logical addressing and routing of data packets between different devices on a network. It is responsible for routing data packets from one device to another based on the destination IP address.
The network layer provides logical addressing through IP addresses, which are unique and assigned to each device on the network. This allows for identification and communication between devices. The network layer also provides routing services through routing protocols such as OSPF, BGP, and RIP. These protocols determine the best path for data packets to travel from the source device to the destination device.
The network layer is also responsible for providing fragmentation and reassembly of data packets. This means that if a packet is too large to be transmitted over a particular link, the network layer will fragment the packet into smaller packets that can be transmitted, and then reassemble the packets at the destination.
Examples of devices that work at the network layer include routers and gateways. Network layer protocols include IP (Internet Protocol), IPv6 (Internet Protocol version 6), ICMP (Internet Control Message Protocol), and IGMP (Internet Group Management Protocol).
In short, the network layer of the OSI model provides logical addressing, routing services and fragmentation and reassembly of data packets between different devices on a network. It uses IP addresses and routing protocols to determine the best path for data packets to travel from the source device to the destination device.
What are the services provided by network layer?
The network layer of the OSI model provides several services that to successfully exchange data between various network devices. These services include:
- Logical Addressing: The network layer provides logical addressing through IP addresses, which are unique and assigned to each device on the network. This allows for identification and communication between devices.
- Routing: The network layer is responsible for routing data packets from one device to another based on the destination IP address. It uses routing protocols, such as OSPF, BGP, and RIP, to determine the best path for data packets to travel from the source device to the destination device.
- Path selection: The network layer is responsible for selecting the best path for the data to reach the destination. It uses metrics such as hop count, delay, bandwidth, and reliability to determine the optimal path.
- Fragmentation and Reassembly: The network layer is responsible for fragmentation and reassembly of data packets. This means that if a packet is too large to be transmitted over a particular link, the network layer will fragment the packet into smaller packets that can be transmitted, and then reassemble the packets at the destination.
- Congestion Control: The network layer is responsible for controlling the amount of traffic on the network, to prevent congestion and ensure efficient use of network resources.
- Quality of Service (QoS): The network layer provides Quality of Service (QoS) features such as traffic shaping, prioritization and reservation of bandwidth to ensure that certain types of traffic receive a certain level of service.
- Error Handling: The network layer is responsible for handling errors that occur during the transmission of data packets. It uses error-handling mechanisms such as ICMP (Internet Control Message Protocol) to inform the source device of any errors that occurred during transmission.
In short, the network layer provides several services that enable the successful transmission of data between different devices on a network. These services include Logical Addressing, Routing, Path selection, Fragmentation and Reassembly, Congestion Control, Quality of Service and Error Handling. These services are essential for the proper communication and coordination of devices on a network and for the successful routing of data packets between devices.
Which protocols use network layer?
The network layer of the OSI model is responsible for providing logical addressing and routing of data packets between different devices on a network. Several protocols are used at the network layer to control these functions and enable successful communication between devices. Some examples of these protocols include:
- IP (Internet Protocol): This is the most widely used network layer protocol. It provides logical addressing through IP addresses and is responsible for routing data packets between devices on a network.
- IPv6 (Internet Protocol version 6): This is the latest version of IP and it was designed to address the limitations of IPv4 and to support a much larger number of devices on the internet.
- ICMP (Internet Control Message Protocol): This protocol is used by network devices, such as routers, to send error messages and operational information indicating success or failure when communicating with other IP enabled devices.
- OSPF (Open Shortest Path First): This is a routing protocol used by routers to determine the best path for data packets to travel through a network.
- BGP (Border Gateway Protocol): This is a routing protocol used to exchange routing information between routers in different autonomous systems (AS) on the internet.
- RIP (Routing Information Protocol): This is a simple distance-vector routing protocol that is used in small and medium-sized networks.
- IGMP (Internet Group Management Protocol): This protocol is used by IP hosts to report their multicast group memberships to any neighboring multicast routers.
In summary, many protocols use the network layer of the OSI model, some examples are IP, IPv6, ICMP, OSPF, BGP, RIP and IGMP. Each protocol provides different services to the network layer such as logical addressing, routing, error handling and others, allowing the efficient and correct communication and coordination of devices on a network.
4. Transport Layer (Layer 4)
The transport layer of the OSI (Open Systems Interconnection) model is the fourth layer and is responsible for providing end-to-end communication and ensuring the reliability of data transfer between devices on a network.
It is responsible for breaking up data into smaller units called segments, and then reassembling them at the destination. It also provides flow control to ensure that the data is transmitted at a rate that the receiving device can handle, and error control to ensure that the data is transmitted correctly.
The transport layer provides two types of services: connection-oriented and connectionless. In connection-oriented service, a virtual circuit (VC) is established between the source and destination devices before data is transmitted. This ensures that data is transmitted reliably and in order. In connectionless service, no virtual circuit is established before data is transmitted. It’s faster but less reliable than connection-oriented service.
Examples of transport layer protocols include TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). TCP is connection-oriented and provides reliable, in-order delivery of data, while UDP is connectionless and provides faster, unreliable delivery of data.
In short, the transport layer of the OSI model provides end-to-end communication and ensures the reliability of data transfer between devices on a network. It provides flow control, error control, and connection-oriented and connectionless services to ensure that data is transmitted correctly and efficiently.
What services are provided by transport layer?
The services provided by the transport layer include:
- End-to-end data transfer: The transport layer ensures that data is delivered correctly and completely from the sender to the receiver.
- Error checking and correction: The transport layer detects and corrects errors that may occur during data transfer.
- Flow control: The transport layer regulates the rate of data transfer to prevent overwhelming the receiving device.
- Multiplexing/demultiplexing: The transport layer allows multiple applications to share the same network connection by separating and reassembling their data.
- Congestion control: the transport layer regulates the amount of data sent to prevent network congestion
- Reliability: the transport layer can ensure that the data sent is received by the receiver.
The most common transport layer protocols are TCP and UDP.
Which protocols use transport layer?
The most common protocols that use the transport layer are TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
- TCP: It is a connection-oriented protocol that provides reliable, ordered delivery of data. It establishes a virtual connection between the sender and receiver before data transfer, and uses a three-way handshake to initiate and terminate the connection. It also uses flow control and error checking to ensure data integrity.
- UDP: UDP on the other hand, is a connectionless protocol that does not establish a virtual connection before data transfer. It does not guarantee the delivery of data, but it is faster and requires less overhead than TCP. It is often used for real-time applications such as streaming video and audio, where the loss of a few packets is not critical.
Other transport layer protocols include SCTP (Stream Control Transmission Protocol) and DCCP (Datagram Congestion Control Protocol).
5. Session Layer (Layer 5)
The session layer is the fifth layer of the OSI (Open Systems Interconnection) model, and it is responsible for establishing, managing, and terminating communication sessions between applications. It controls the dialogues between computers and synchronizes their communication. The session layer allows two applications to establish a connection and exchange data in a coordinated and orderly way.
It also provides the capability to initiate, maintain, and terminate connections between network devices. The session layer is responsible for creating and maintaining a session between applications, which is a logical communication channel that allows them to exchange data. It is not a widely used layer, instead, the functions of the session layer are often combined with the application layer.
What are the services provided by session layer?
The services provided by the session layer include:
- Connection establishment and termination: The session layer establishes, maintains, and terminates connections between applications, allowing them to exchange data in a coordinated and orderly way.
- Synchronization: The session layer synchronizes the communication between applications, ensuring that data is exchanged in the correct order and that no data is lost.
- Dialog control: The session layer controls the dialog between applications, ensuring that they are able to exchange data in a meaningful way.
- Token management: In some cases, the session layer also manages token that is used to grant access to shared resources.
- Checkpointing: The session layer can periodically save the progress of a conversation, so that it can be resumed after an interruption.
It’s worth noting that the Session layer is not widely used in modern network stack and its functionality is often combined with the application layer, for example in the TCP/IP model, session layer functionality is not included.
Which protocols use session layer?
The Session layer is not widely used in modern networks, and it is not a well-defined layer in most of the widely used network models such as TCP/IP. The Session layer is part of the OSI (Open Systems Interconnection) model, which is mainly used in academic and theoretical contexts, but not in actual networking implementations. As a result, there are not many protocols that are specifically designed to use the session layer.
Some protocols that may be associated with the session layer include:
- Remote Procedure Call (RPC) which is used to initiate and manage remote procedure calls in distributed systems.
- NetBIOS (Network Basic Input/Output System) which is used to provide session-layer services for applications that run on top of the NetBEUI (NetBIOS Extended User Interface) transport protocol.
- NFS (Network File System) which is used to provide file-sharing services in a networked environment.
In general, the session layer is not widely used and its functionality is often combined with the application layer in modern networks.
6. Presentation Layer (Layer 6)
The presentation layer is the sixth layer of the OSI (Open Systems Interconnection) model, and it is responsible for the syntax and semantics of the information exchanged between devices. It provides a common format for the data so that it can be understood by both the sender and the receiver. The main function of the presentation layer is to convert data from the application into a format that can be transmitted over the network, and then convert it back into a format that can be understood by the receiving application.
It is also responsible for data compression, encryption and decryption, and convert the data into a format that the application can understand. It also helps to deal with data integrity to ensure the data being sent is the same as the data being received.
It’s worth noting that, like the session layer, the Presentation layer is not widely used in modern network stack and its functionality is often combined with the application layer, or handled by the operating system or the application itself.
What are the services provided by presentation layer?
The services provided by the presentation layer include:
- Data conversion: The presentation layer converts the data from the application into a format that can be transmitted over the network, and then converts it back into a format that can be understood by the receiving application.
- Data compression: The presentation layer can compress data to reduce the amount of bandwidth required for transmission, and then decompress it at the receiving end.
- Data encryption: The presentation layer can encrypt data to protect it from unauthorized access or tampering during transmission, and then decrypt it at the receiving end.
- Data integrity: The presentation layer can ensure the data being sent is the same as the data being received by adding checksums or other validation methods.
- Character code translation: The presentation layer can translate between different character encodings, such as ASCII and Unicode, to ensure that text data can be understood by the receiving application.
It’s worth noting that, like the session layer, the Presentation layer is not widely used in modern network stack and its functionality is often combined with the application layer, or handled by the operating system or the application itself.
Which protocols use presentation layer?
The Presentation layer is not a well-defined layer in most of the widely used network models such as TCP/IP, and it is not widely used in modern networks. As a result, there are not many protocols that are specifically designed to use the presentation layer.
Some protocols that may be associated with the presentation layer include:
- ASN.1 (Abstract Syntax Notation One) which is used to define a formal notation for describing data structures.
- XDR (External Data Representation) which is used to define a standard format for data that is exchanged between different systems.
- PEM (Privacy Enhanced Mail) which is used to encrypt email messages for secure transmission.
In general, the presentation layer is not widely used and its functionality is often combined with the application layer or handled by the operating system or the application itself.
7. Application Layer (Layer 7)
The application layer is the seventh and highest layer of the OSI (Open Systems Interconnection) model, and it is responsible for providing interfaces and protocols that allow applications to access the network’s resources. It provides the means for applications to communicate with each other and with the network. The application layer provides a variety of services that are specific to different types of applications, such as file transfer, email, and web services.
It defines the protocols and interfaces that allow application programs to access network services and resources. Application layer protocols provide a common set of rules and conventions that enable different applications to communicate with each other.
Examples of application layer protocols include HTTP (Hypertext Transfer Protocol) for web services, FTP (File Transfer Protocol) for file transfer, SMTP (Simple Mail Transfer Protocol) for email, and DNS (Domain Name System) for translating domain names to IP addresses. Other examples include SSH (Secure Shell) for secure remote access, and Telnet for remote terminal access. These protocols are designed to be used by specific types of applications and are independent of the underlying network.
It’s worth noting that, depending on the network model or stack, the functionality of the presentation, session and application layers could be combined in a single layer.
What are the services provided by application layer?
The services provided by the application layer include:
- Application-specific services: The application layer provides a variety of services that are specific to different types of applications, such as file transfer, email, and web services.
- Interface to network services: The application layer provides the means for applications to communicate with each other and with the network, through a set of protocols and interfaces that allow application programs to access network services and resources.
- Network access and resource sharing: The application layer enables applications to access and share network resources, such as files, printers, and databases.
- User authentication and authorization: The application layer can provide mechanisms for authenticating users and controlling their access to network resources.
- Network management: The application layer can provide tools and protocols for managing and monitoring the network, such as SNMP (Simple Network Management Protocol).
- Interoperability: The application layer provides a common set of rules and conventions that enable different applications to communicate with each other, regardless of their underlying technology.
It’s worth noting that, depending on the network model or stack, the functionality of the presentation, session and application layers could be combined in a single layer and the list of services provided by application layer could vary.
Which protocols use application layer?
The Application layer is the highest layer of the OSI (Open Systems Interconnection) model and it provides a variety of services that are specific to different types of applications. There are many different protocols that use the application layer, some examples include:
- HTTP (Hypertext Transfer Protocol) – used for web services, which allows clients and servers to communicate and transfer web pages.
- FTP (File Transfer Protocol) – used for transferring files between computers.
- SMTP (Simple Mail Transfer Protocol) – used for sending and receiving email messages.
- DNS (Domain Name System) – used for translating domain names to IP addresses.
- SSH (Secure Shell) – used for secure remote access to servers and network devices.
- Telnet – used for remote terminal access to network devices.
- SNMP (Simple Network Management Protocol) – used for managing and monitoring network devices.
- POP3 (Post Office Protocol version 3) – used for receiving email messages from a mail server.
- IMAP (Internet Message Access Protocol) – used for managing email messages on a mail server.
- DHCP (Dynamic Host Configuration Protocol) – used for automatically assigning IP addresses to devices on a network.
These protocols are designed to be used by specific types of applications and are independent of the underlying network. Depending on the network model or stack, the functionality of the presentation, session and application layers could be combined in a single layer and the list of protocols used by application layer could vary.
Some Popular Switches by different manufacturers
Taking into account the definitions of the layer 2 and layer 3 switches, we can determine what fits a company’s budget the most.
Some of the most popular Layer 2 and Layer 3 switches are:
- Cisco Catalyst Series: Cisco’s Catalyst series of switches are widely used in enterprise networks. They offer a wide range of features, including advanced security, Quality of Service (QoS), and Power over Ethernet (PoE). There are various series that support Layer 2 switching:
- HP Aruba Series: HP’s Aruba series of switches are also popular in enterprise networks. They offer a similar set of features as the Cisco Catalyst series and are known for their reliability and ease of use.
- Juniper EX Series: Juniper’s EX series of switches are popular in service provider networks and offer high-performance and scalability. They also provide advanced features such as virtual routing and security.